How to Hack Instagram
Table of content
Instagram was originally launched for the iPhone in 2010. Over time, it gained popularity, and Facebook owned it, and an Android version also came. This app is really interesting. You can make your videos, post your pictures, or make your own video using different pictures while choosing background music from the Instagram library. It has many filters both for pictures and videos.
Did you ever think about hacking an Instagram account? Why did you think so? Was that for monitoring your kids? Or tracking your employee's social media activities, or you were suspicious about your partner's activities? The reason could be any of them but knowing how to hack an Instagram account is still an unanswered question. Let us first discuss the reasons for hacking someone's account, and then we will let you know how to hack Instagram.

Part 1. Why Do People Hack an Instagram Account
Once you decide to hack an Instagram account, you don't retrieve it even if you know sometimes curiosity kills the cat. Knowing your kids are using social media apps, your employees are also interacting through it, and your partner might be interested in someone. With all those fears in mind, you cannot sit calmly and silently. In any case, you have to encounter the truth, and for this, you need evidence. Especially when you have all the right reasons to do so, let's catch up to know them.

To Keep Kids Safe On Instagram
Instagram accounts are easily connected to other applications, for example, Clubhouse, Facebook etc. Social media is vast, and your child cannot foresee the dangers. To prevent your kid from cyberattacks, you have the right to hack their account. You can reach other accounts through the Instagram account and monitor their social media activities.
To Spy On Suspicious Spouse
You are watching your spouse's behaviour noticeably change. You cannot sit comfortably on your couch and let that happen. To protect your relationship till the last try is what a rational and loyal person would do. It might be your misunderstanding, but what if it is true. You need a base to face your partner. You want to do something about it. You have no option other than to spy on them.
To Spy On Employees
Running an organisation is the tip of the iceberg. Apart from other millions of problems, your employees are at your wits' end. Monitoring each of them is your duty which is not an easy task. supposedly they should be working honestly for your company, but what if they are watching a movie during office hours or chatting with friends through social media. You are left with the option of spying on them to maintain and improve the quality of work.
To Access Confidential Information
Some people rely on professional hackers to spy on a targeted person. An investigator has to hack an account to get confidential information to pursue his case. Similarly, police or FBI agents have the right to hack Instagram accounts.
Part 2. How to Hack Instagram Account
Now we have all the knowledge for the reasons to hack Instagram accounts. Now next, we have to find out the ways.

1. Using the Spy app
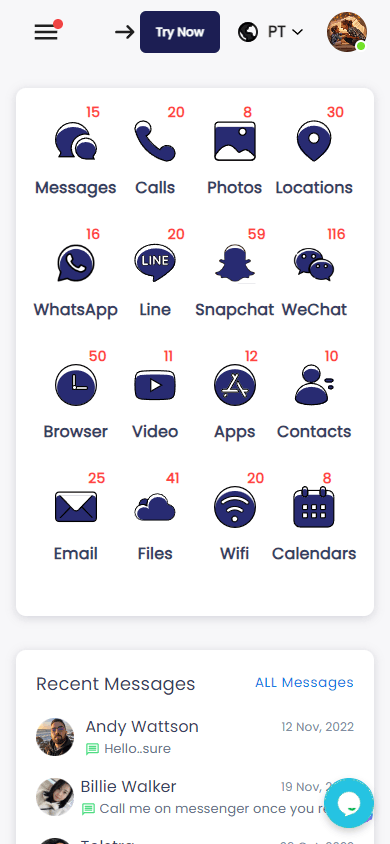
It is one of the safest ways to hack an account. One of the best Android&iOS spy apps is SpyX. It is declared the best parental control app of 2022, with 4.8 ratings. Its features and economical purchasing plans distinguish this app from other apps.
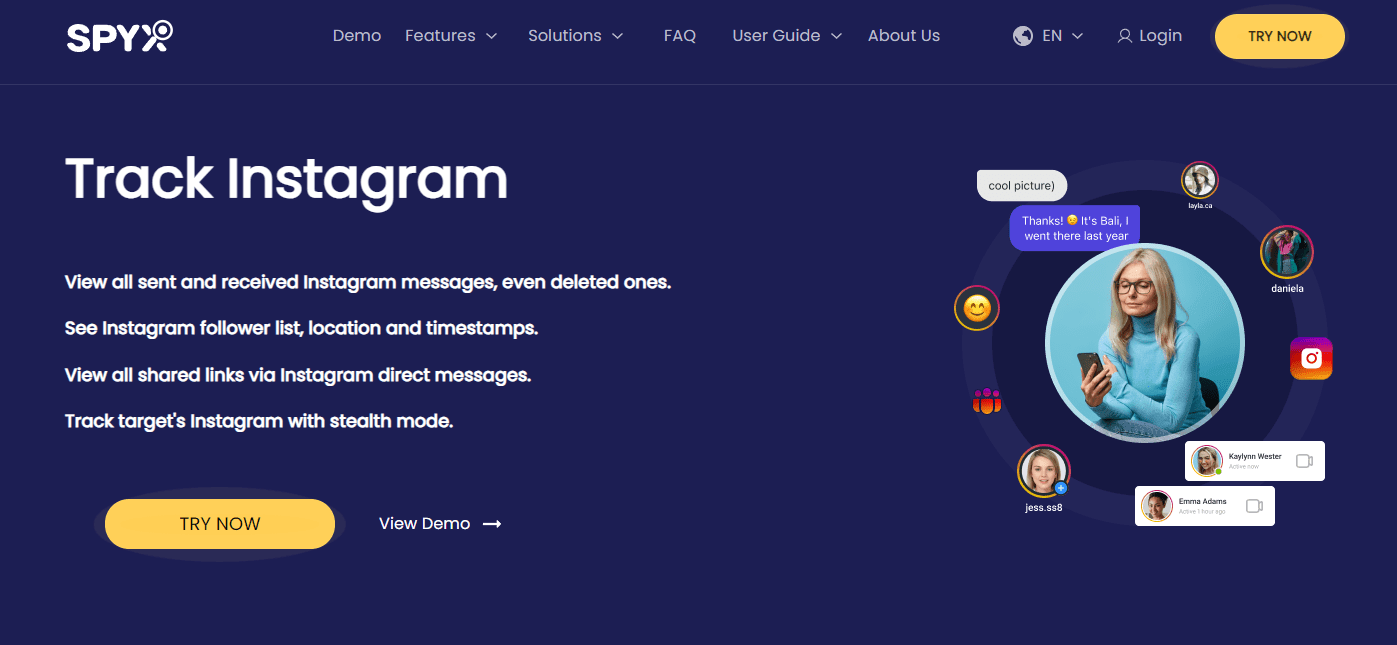
Some of the highlighted features are:
- Monitoring of every keystroke and Tap
- Tracking where the targeted person is going
- Finding out who the targeted person is calling
- Tracking of browsing history
- Reading social media chats
- Reviewing of text, including deleted messages
- Monitoring of received and sent videos and photos
- Do it all without being detected
- Compatibility with all iOS&Android devices
How to use SpyX to hack Instagram
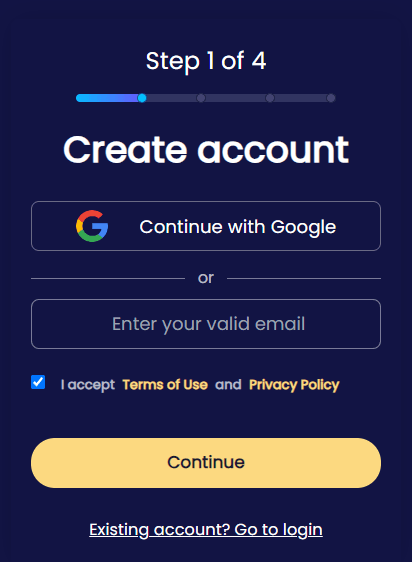
Step 1. Create a free account with valid email/Google account.
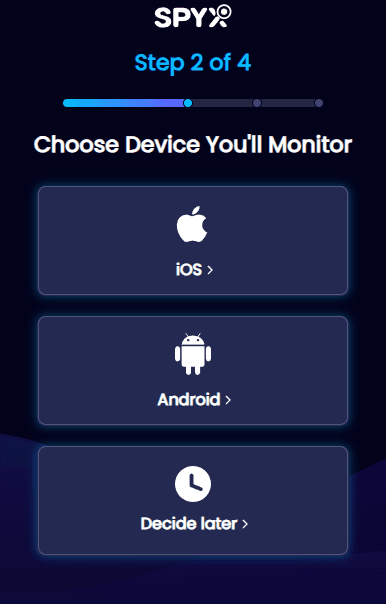
Step 2. Connect kid's iPhone/Android with SpyX.
Step 3. Log in to your SpyX dashboard, and you can view Instagram of traget device.
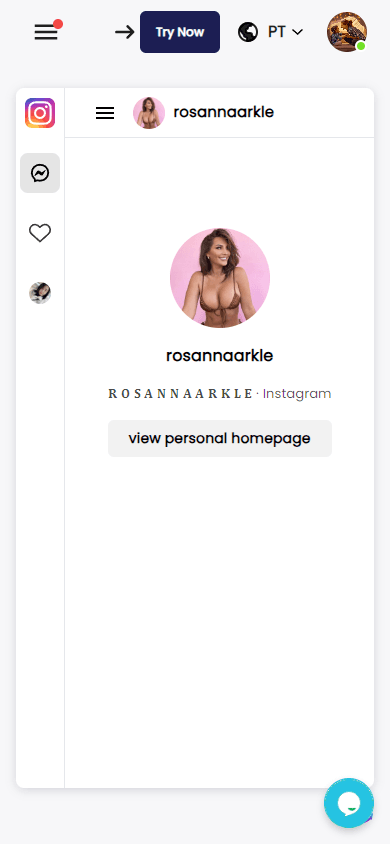
Step 4. You can also track photos, GPS locations, social app chats (WhatsApp messages, Instagram, Snapchat, etc.)
You need physical access to the targeted device for the first time. Once it is bind with SpyX, you are good to go without being detected. You have your control panel to control everything.
2. Phishing technique
Like a fish is trapped through bait, the same is the case with phishing. Hackers use this trick to tempt the user and hack their accounts. Suppose an email asks you to enter your personal information and might have instructions. If you don't do that, your account might get deleted. Moreover, it might ask you to log in through your email and password; the moment you press done, your account gets hacked.

3. Using Keyloggers
Keyloggers are the most used malware for Instagram. Hackers record all your taps through a keylogger. In short, if one keylogger application or software is installed, it becomes very easy to know a user's password and bank information.
4. Brute Force
Brute force is a process in which a hacker tries to guess the user's password until he gets the real one. It does not go successfully with Instagram. Instagram has a built-in feature for protecting an account. It identifies and blocks repeated attempts to reach an account using incorrect passwords.
Part 3. Conclusion
Hacking an Instagram account is not that difficult. Make sure you use these methods to save your loved ones and subordinates. Hacking for malicious purposes is always a sin and a crime. Suppose your Instagram account is hacked and deleted. You have thirty days to recover it through meta(Facebook). It is better to contact the Instagram help service immediately.
More Articles Like This







Disclaimer: SPYX'S SOFTWARE INTENDED FOR LEGAL USE ONLY. You are required to notify users of the device that they are being monitored. Failure to do so is likely to result .....
Registered Address: South Bank Tower, 55 Upper Ground,, London, England, SE1 9EY
Company Name: UK GBYTE TECHNOLOGY CO., LIMITED
Wisteria Trade Limited
