The complete guide to iCloud track: Prevention, detection and recovery
Last updated:mars 25, 2025
Table of content
Having an uncomfortable outlook on the wellbeing of your iCloud account? The quantity of internet based dangers is developing, so you ought to improve your computerized protections against potential assailants. Envision receiving a stressing message that somebody is breaking into your iCloud.
Yet, sit back and relax! This article discusses a great deal of well known ways programmers get into iCloud. It additionally guides you assuming your record is tracked and how to guard it. Go out traveling to keep your computerized safe spot safe and prevent others from getting to it.
Part 1. What is iCloud track
"iCloud track" implies that somebody got into your record without your consent. Trouble makers can get in many ways, for example, through security openings, tricks, and spy applications.
On the off chance that somebody gets into your iCloud account, they can take your documents, photographs, and confidential information.
What could turn out badly on the off chance that somebody gets into iCloud? Somebody could break into your home, take your name, or prompt you to lose cash. You really want to comprehend how iCloud tracks work to safeguard your records and mystery subtleties.
Part 2. 4 common ways that trackers track iCloud account
In this section, I'll discuss the four most common methods trackers use to access iCloud accounts, focusing on spy application as the most challenging to defend against. I'll also provide detailed explanations of the other three methods to help you better understand iCloud tracks.
Way 1. Spy applications
Programmers use spy applications, which are otherwise called spyware, to get into individuals' iCloud accounts without their consent. These sorts of unsafe applications get on gadgets without the client's information and begin to work. This allows programmers to keep an eye on the gadget and take private data. To realize how spy applications work, what highlights they have, and how to utilize them, this is an ideal aide for you.
What is a spy app
Spy applications were first made for good reasons, such as watching out for laborers or children. However, programmers are involving them for terrible things to an ever increasing extent. You can guilefully put these applications on PCs, tablets, telephones, and different devices so others can keep an eye on them and take their information.
How does a spy application work
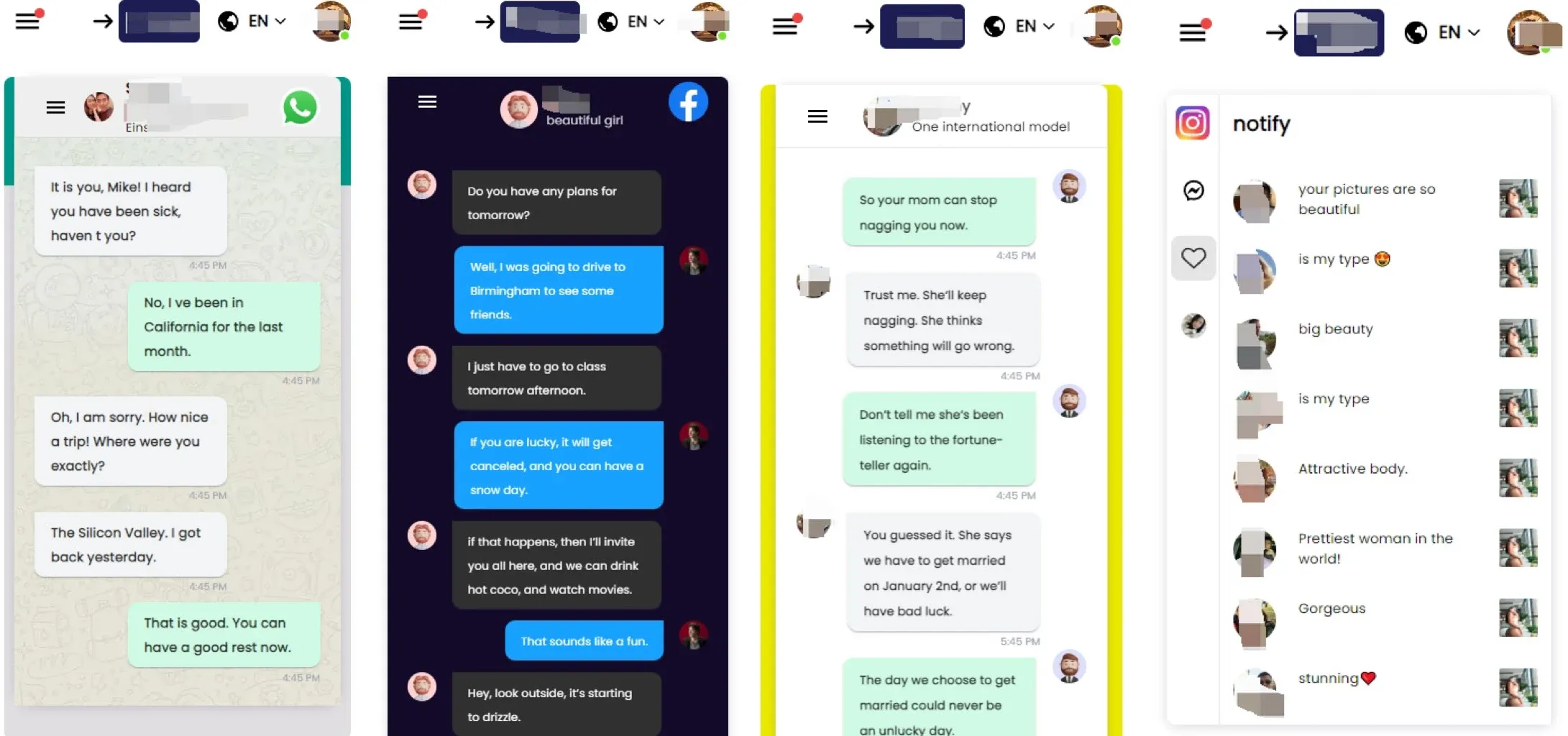
Once an application is on a gadget that is being kept an eye on, it works behind the scenes without the proprietor of that gadget monitoring it. It can get to call logs, instant messages, the web foundation, your GPS area, and your virtual entertainment action, in addition to other things. The data is then shipped off a server in a better place that is overseen by programmers. On the off chance that somebody tracks in, they can see the data through an electronic screen or a portable application.
Features of spy applications
Many pieces of spy applications are made to assist programmers with doing what they need to do. Here are a few things that are similar:
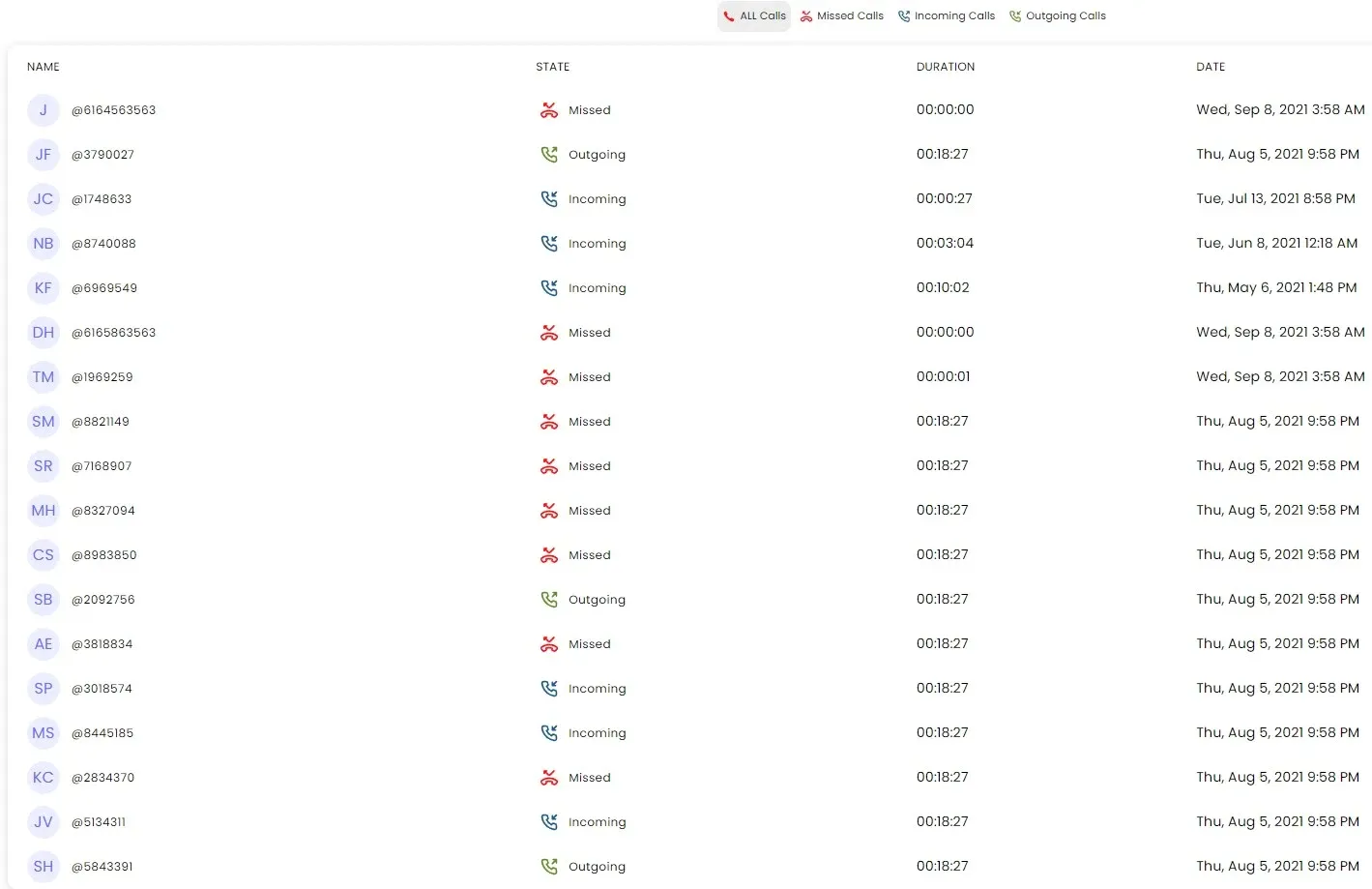
When you use spy applications, you can record both approaching and active calls, as well as subtleties can imagine the time and length of the call.Text Message Following: Regardless of being erased, they can in any case peruse and record instant messages sent and got by the objective gadget.
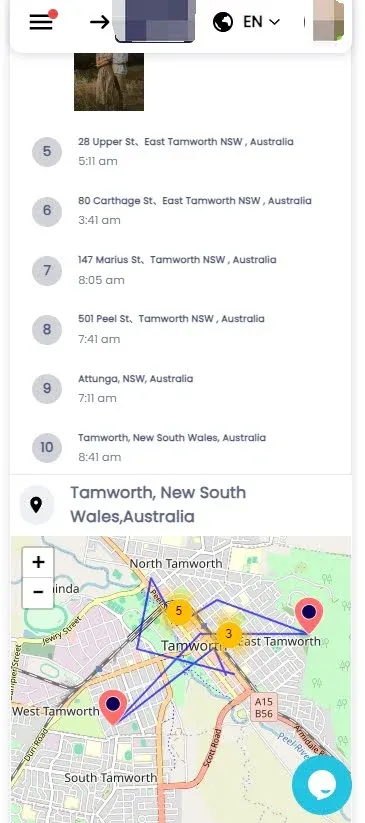
Spy applications can utilize GPS to constantly know where the gadget is, allowing programmers to watch out for what the client does.
Individuals who follow you on Facebook, Instagram, WhatsApp, and Snapchat can see your posts, visits, photographs, and different exercises on those locales.
Keyloggers in a portion of the more remarkable covert operative applications record each snap on the gadget. There is private information in it, as usernames, passwords, and that's only the tip of the iceberg.
Steps of utilizing spy applications
Using phone spyware typically involves purchasing and downloading the software onto the target device. Once installed, the spyware can be remotely accessed and controlled by the person who installed it.
The spyware operator can view, track, and store the user activities and data of the targeted devices, including call logs, text messages, browsing history, GPS location, and more, without the user's knowledge or consent.
This kind of software is often used for parental monitoring, employee monitoring, or in more nefarious cases, for spying on individuals without their awareness.
Way 2. Phishing assaults
Individuals offer their iCloud login data when they get phony messages or visit counterfeit sites. Cybercriminals send counterfeit messages that appear to come from Apple or a notable specialist co-op. The messages have counterfeit documents or connections inside them. There is a trick where clients are deceived and their iCloud username and secret key are saved as they type them into counterfeit login screens.
Way 3. Beast power assaults
They continue to attempt to sign in until they hit the nail on the head. We call this a savage power assault. These instruments let you immediately think of and evaluate many thousands or even large number of potential passwords. At the point when utilized as a track, savage power works best on passwords that are feeble or simple to sort out. Ensure your passwords are solid and difficult to figure for your iCloud accounts.
Way 4. Security weaknesses
Programmers can get into individuals' records without their consent on the off chance that iCloud or administrations that work with it don't have great insurance. These openings could show up on account of how security is set up off-base, programming bugs, or settings that don't seem OK. Criminals can get into iCloud accounts on the off chance that they can find and utilize these security openings. In the event that you stay up with the latest, make security changes, and mind things frequently, somebody is less inclined to utilize a security opening against you.
To lay it out plainly, you want to know how programmers generally get into iCloud records to keep yours safe. Terrible individuals will actually want liable to have the option to get into your iCloud account without your authorization assuming you are familiar the dangers and do whatever it takes to safeguard it. This will safeguard your confidential data and advanced things.
Part 3. Signs your iCloud account might be tracked
Do you suppose somebody got into your iCloud account? Look out for these things.
● Unapproved access:
You didn't give anybody access to your iCloud account, which is an obvious indicator that it has been tracked. On the off chance that you can't sign in or gadgets that are connected with your iCloud account work right, somebody presumably got in without your consent.
● Dubious messages or messages:
Assuming somebody gets into your iCloud account, they will frequently send counterfeit messages or notes to individuals in your location book. Assuming family or companions say they received weird messages or messages from your record that you didn't send, almost certainly, somebody got in without your authorization.
● Unexplained changes:
In the event that your secret word, security questions, or reinforcement email address change for reasons unknown, somebody has changed the settings for your iCloud account. They could change these settings to watch out for your record and make it unimaginable for you to sign in once more.
● Missing or erased information:
You could have lost iCloud records, photographs, or different things. Somebody could change or eliminate private data in your record without your insight. Along these lines, they would feel lost and open to hurt.
● Dubious gadget action:
Assuming that the gadgets you're connected to do abnormal things, similar to crash or run gradually, or on the other hand assuming they show bizarre messages, you ought to look at them. Something awful may be running behind the scenes and seriously jeopardizing your gadget assuming these things occur.
● Expanded information utilization:
Somebody could get into your iCloud account and send or store a ton of information. This would out of nowhere make your information utilize go up. A great deal of data might be being utilized for not an obvious explanation. Check whether another person is utilizing your record simultaneously.
● Account lockouts or suspensions:
Your Apple ID might be briefly locked or suspended assuming Apple sees weird endeavors to sign in or conduct that ought not be occurring. If you get texts expressing that your record isn't secure or that you can't get to your iCloud account, you ought to look all the more carefully for indications of tracking.
Part 4. The most effective method to shield your iCloud from tracks
To safeguard your delicate information and web security, you should safeguard your iCloud account. To protect your iCloud from programmers, here are a few things you can do now:
● Empower Two-Variable Verification (2FA):
To get into your iCloud account, you want two methods for demonstrating what your identity is: your secret key and a code shipped off your telephone. It's currently far better. Somebody could get in regardless of whether they know your secret word, yet provided that you permit them to; that is 2FA.
● Utilize solid passwords:
Individuals who need to track into your iCloud record will struggle assuming you utilize solid, one of a kind passwords. You don't need to utilize dates, notable expressions, or library words. To make it considerably harder to sort out, utilize a blend of all shapes and sizes letters, numbers, and extraordinary characters.
● Consistently update passwords:
Individuals will not have the option to get into your iCloud account without your consent assuming you change your secret phrase frequently. You can utilize apparatuses to assist you with making safe passwords and recollect them. You ought to likewise change your passwords immediately assuming you think somebody has tracked your record or accomplished something different bizarre.
● Be careful about phishing endeavors:
Don't open connections or snap on records in messages, messages, or spring up cautions that request individual data or believe that you should sign in to your iCloud account. Watch out for tricks, and check texts before you do anything.
● Keep programming refreshed:
It is essential to constantly have the latest security patches and programming reports on the entirety of your gadgets, working frameworks, and applications that utilization iCloud. Staying aware of Mac's progressions is essential to fix known bugs and hold programmers back from utilizing your PC.
● Screen record movement:
There could be things happening with your iCloud account that you didn't do or change. To make certain of this, really take a look at your record settings and conduct constantly. Watch out for what you've been doing, the gadgets that are connected, and your login data. This will help you find and fix any conceivable security gambles rapidly.
● Utilize trusted gadgets and organizations:
Programmers could possibly see or get your passwords on the off chance that you sign in to your iCloud account on a public or free Wi-Fi organization. Assuming that you just utilize safe gadgets and web interfaces, nobody will actually want to get into your record without your consent.
● Teach yourself about security practices:
Figure out how to safeguard your iCloud account in the most effective ways as new dangers show up. Realize tracking stunts, counterfeit tricks, and web security. This will make it doubtful that somebody will track you or your loved ones.
Part 5. What to do on the off chance that your iCloud is tracked
Somebody has broken into your iCloud account. It's terrifying to contemplate, however you want to act rapidly to stop the harm and oversee your record. These means ought to be taken on the off chance that you think somebody has gotten into your iCloud:
● Change your secret phrase:
Now is the ideal time to change your iCloud secret word. Do it now to succeed. Try not to involve a similar secret word for more than one record. Make major areas of strength for a that has never been utilized. Assuming you do this, no other person will actually want to get into your record without your authorization. Right now is an ideal opportunity to change your secret key.
● Empower Two-Component Validation (2FA):
Two-factor confirmation (2FA) ought to be turned on for your iCloud account on the off chance that it isn't now. With 2FA, you really want something other than your secret phrase to show what your identity is. As an additional method for showing what your identity is, you could get a code on your telephone. This helps ensure that somebody can't get in without your authorization regardless of whether they know your secret word.
● Survey your record movement:
Your iCloud record and settings might have been watched or changed by another person. Check them frequently to ensure. Verify whether your record is connected to any unusual devices in the event that you just signed in. Ensure that none of your security or settings have changed in a manner that doesn't check out.
● Contact Apple backing:
When you suspect that somebody has broken into your iCloud account, you ought to find support. To guard your record, Apple representatives can help you, investigate any bizarre movement, and give you tips on the most proficient method to assume back command over your record.
● Eliminate unapproved gadgets:
Dispose of any gadgets that are associated with your iCloud account immediately. To do this, go to the settings for your iCloud record and block any gadgets you don't have the foggiest idea or trust.
● Screen your records:
Screen your different gadgets and online records to check whether they are acting entertaining or on the other hand assuming somebody is getting into them without your award. Terrible individuals could attempt to involve defects in more than one record, so you should know about and responsible for your web-based life.
● Instruct yourself:
Find out about tracks, counterfeit arrangements, and the most secure ways of keeping your data. Remain informed about new security risks and do whatever it may take to stop them before they occur. This will bring down your gamble of being tracked.
Part 6. Forestalling future iCloud tracks
To protect your iCloud account from programmers, you ought to continuously watch out. The accompanying things are important to hold others back from getting into your record:
● Routinely update passwords:
You ought to change your iCloud secret word frequently assuming you utilize a similar one for more than one record. Programmers will make some harder memories breaking solid passwords that are comprised of a blend of letters, numbers, and unique characters
● Empower Two-Variable Verification (2FA):
To make your iCloud account much more secure, ensure that two-factor insurance is turned on. Somebody who needs to get into your record will require both your secret word and a two-factor confirmation code.
● Be mindful of phishing endeavors:
Locales, messages, or messages that request your iCloud login data ought not be ready to get it from you. Individuals who need to take your data could attempt to get it from you when you click on bizarre connections or download documents from individuals you don't have any idea.
● Keep programming refreshed:
Ensure that the entirety of the gadgets, applications, and working frameworks you use with iCloud have the latest security fixes and changes. This safeguards you from known openings in your security that programmers could utilize.
● Screen record action:
Consistently check your iCloud settings and how it attempts to check whether you rolled out any improvements or moves that you didn't intend to. Watch the gadgets you've connected, your login data, and what you've been doing recently to remain safe.
● Utilize confided in organizations:
Clients who interface with a public or unstable Wi-Fi network while signed in to iCloud could possibly see or get your passwords. Everybody will require your authorization to get into your record after that. On the web, use connections and organizations that are protected.
● Instruct yourself:
The most up to date web risks and the most ideal ways to guard your iCloud account are made sense of here. Programmers and tracking tricks have a great deal of casualties. Programmers are bound to target individuals who have some familiarity with these things.
Part 7. FAQs about iCloud track
Q1. Might somebody at any point track my iCloud account?
Programmers, individuals who utilize sheer power, or individuals who search for security holes could get into your iCloud account without you knowing.
Q2. How can I say whether my iCloud account has been tracked?
A programmer has gotten into your iCloud account in the event that somebody composes or gets weird messages or messages from your record, changes your record settings in a way you can't make sense of, erases information, or makes your gadget act in an unusual manner.
Q3. How would it be advisable for me to respond assuming I suspect my iCloud account has been tracked?
Would it be advisable for you suspect that somebody has gotten to your iCloud account, you ought to speedily change your secret phrase, turn on two-factor verification, explore how has been managed your record, remove any gadgets that ought not be there, and contact Apple Backing for help.
Q4. How might I forestall future tracks on my iCloud account?
To protect your PC, utilize two-factor login constantly, ensure your product is exceptional, watch your record, just associate with networks you know, and find out about the most current measures.
Q5. Is it protected to store delicate data on iCloud?
Utilize solid passwords, empower two-factor confirmation, and know about the dangers, regardless of whether iCloud safeguards your information.
Part 8. Conclusion
Programmers ought not be ready to get into your iCloud record and take your significant information. It's doubtful that somebody will get into your record without your authorization assuming you utilize solid passwords, turn on two-factor verification, and watch out for tricks.
Change your iCloud passwords frequently and figure out how to guard your record. Simply ensure that your program is dependably exceptional. Being cautious and careful all the time is important for great assurance. You can rest soundly around evening time realizing that awful individuals can't get to your advanced stuff.
More Articles Like This