How to Track Tinder Dating App Without Someone Knowing
Tinder is an incredibly popular dating app that has become part of modern dating culture. However, there are some risks associated with using this dating app. For parents, spouses or employers, these apps can pose some problems. They may worry that their children, spouses or employees will be judged by bad people or will waste time on these apps. Tracking Tinder can help you better protect your family and maintain relationships by helping you understand what your kids or spouse are doing on the platform.

First of all, the influence of dating software on minors is worthy of vigilance. Minors will face various potential dangers, such as being deceived, seduced and sexually harassed. Therefore, parents should pay attention to their children's Tinder usage and take timely measures to protect their children's safety.
Second, for spouses, using Tinder can create a crisis of trust and family strife. So if a spouse suspects their significant other is using Tinder, they might consider tracking the Tinder account to get evidence.
However, Tinder does not allow users to gain unauthorized access to other people's accounts. Methods of tracking Tinder accounts include using third-party software and programs to obtain passwords, or using phishing techniques. These methods may involve violations of laws and pose potential threats to users' own privacy and security.
The influence and diversity of tinder dating software:
Impact on family: If someone in your family uses Tinder, other family members may feel dissatisfied and concerned about their behavior. In addition, if children learn that their parents use tinder, they may have negative emotions and even affect their parents' trust.
Effects on children: Since tinder is an adult social platform, children should not use the app. If children misuse tinder, they may be exposed to inappropriate content and bad information, which will affect their mental health.
Impact on spouses: If a spouse uses tinder, there may be trust issues and family conflicts. In some cases, it can provide an opportunity for infidelity and lead to psychological betrayal.
Impact on employees: If employees use tinder during working hours, it may affect their productivity and work ethics. In addition, if an employee makes inappropriate remarks or leaks confidential company information on tinder, it may have a negative impact on the company.
Regarding the variety and complexity of tinder, it is a dating app that contains various functions. It has many different features like swipe to match, messages, profiles and many more. In addition, Tinder includes advanced features such as "Super Like" and "Rewind," which allow users to find and match other users with greater precision. At the same time, tinder also has some bad aspects, such as fake profiles and fraud. These bad aspects can cause damage to users, so users need to be vigilant.
Part 2. How to Track Tinder Account
Now next, we have to find out the ways.

1. Using the Spy app
It is one of the safest ways to track an account. One of the best spy apps is SpyX. It is declared the best parental control app of 2022, with 4.8 ratings. Its features and economical purchasing plans distinguish this app from other apps.
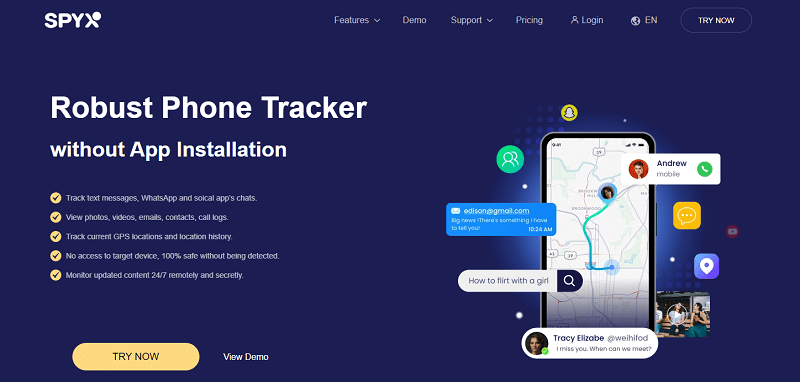
Some of the highlighted features are:
• Monitoring of every keystroke and Tap
• Tracking where is the targeted person going
• Finding out who the targeted person is calling
• Tracking of browsing history
• Reading social media chats
• Reviewing of text, including deleted messages
• Monitoring of received and sent videos and photos
• Do it all without being detected
• Compatibility with all iOS devices
Purchasing a suitable plan is a great option. It offers different plans with different prices. Family package or an individual one. The choice is yours. You can operate it in three easy steps.
Step 1. Create a free account
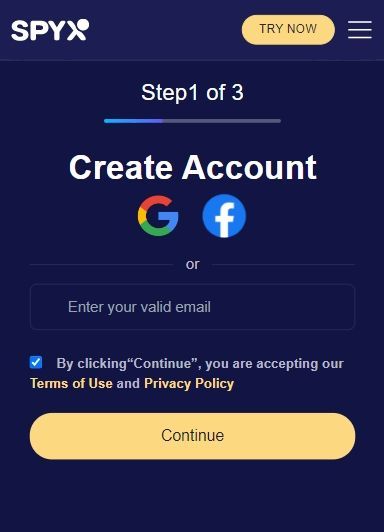
Step 2. Verify target iCloud
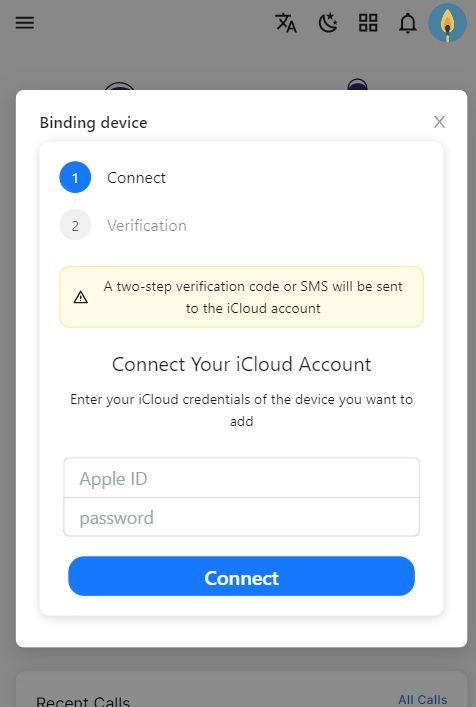
Step 3. Start monitoring and rest is easy
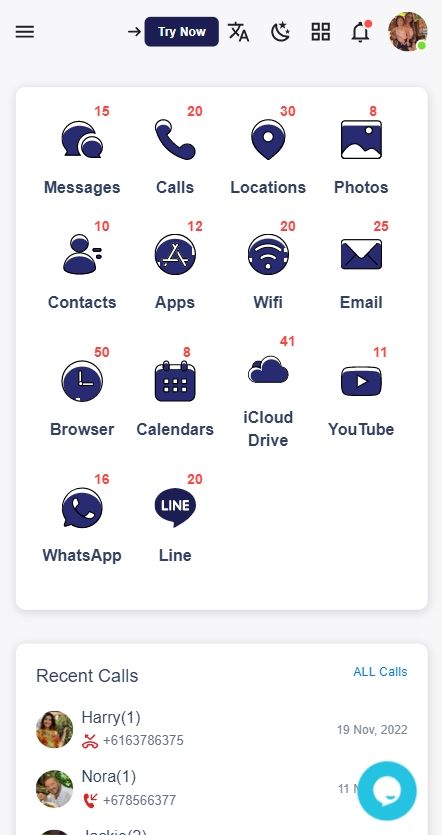
You need physical access to the targeted device for the first time. Once it is bind with SpyX, you are good to go without being detected. You have your control panel to control everything.
2. Phishing technique
Like a fish is trapped through bait, the same is the case with phishing. Trackers use this trick to tempt the user and track their accounts. Suppose an email asks you to enter your personal information and might have instructions. If you don't do that, your account might get deleted. Moreover, it might ask you to log in through your email and password; the moment you press done, your account gets tracked.

3. Using Keyloggers
Keyloggers are the most used malware for Tinder . Trackers record all your taps through a keylogger. In short, if one keylogger application or software is installed, it becomes very easy to know a user's password and bank information.
Rlated: Top 10 Best iPhone Keylogger
4. Brute Force
Brute force is a process in which a tracker tries to guess the user's password until he gets the real one. It does not go successfully with Tinder . Tinder has a built-in feature for protecting an account. It identifies and blocks repeated attempts to reach an account using incorrect passwords.
Part 3. Conclusion
Tracking an Tinder account is not that difficult. Make sure you use these methods to save your loved ones and subordinates. Tracking for malicious purposes is always a sin and a crime. Suppose your Tinder account is tracked and deleted. You have thirty days to recover it through meta(Facebook). It is better to contact the Tinder help service immediately.
More Articles Like This
SPYX'S SOFTWARE INTENDED FOR LEGAL USE ONLY. You are required to notify users of the device that they are being monitored. Failure to do so is likely to result in violation of applicable law and may result in severe monetary and criminal penalties ...
Disclaimer: SPYX'S SOFTWARE INTENDED FOR LEGAL USE ONLY. You are required to notify users of the device that they are being monitored. Failure to do so is likely to result .....







